Exactly How Data and Network Safety And Security Safeguards Against Emerging Cyber Threats
In an era noted by the fast evolution of cyber dangers, the importance of data and network security has never ever been a lot more pronounced. As these risks come to be much more complicated, recognizing the interplay between data protection and network defenses is crucial for minimizing threats.
Understanding Cyber Risks

The ever-evolving nature of modern technology constantly introduces new susceptabilities, making it necessary for stakeholders to stay cautious. Individuals might unconsciously succumb social design tactics, where opponents control them right into divulging delicate information. Organizations face special challenges, as cybercriminals commonly target them to manipulate important information or interfere with operations.
Additionally, the surge of the Internet of Things (IoT) has actually increased the attack surface area, as interconnected gadgets can work as access points for opponents. Recognizing the relevance of robust cybersecurity techniques is essential for alleviating these threats. By cultivating a comprehensive understanding of cyber companies, individuals and dangers can apply effective methods to guard their electronic properties, making certain strength despite an increasingly intricate threat landscape.
Key Components of Data Security
Ensuring information protection calls for a multifaceted approach that incorporates numerous crucial elements. One fundamental element is information security, which changes delicate details into an unreadable layout, accessible only to authorized customers with the proper decryption secrets. This acts as an important line of defense against unauthorized accessibility.
An additional crucial component is accessibility control, which controls who can view or control data. By implementing rigorous individual authentication methods and role-based gain access to controls, organizations can minimize the danger of insider hazards and information breaches.
Additionally, data concealing techniques can be employed to protect delicate details while still permitting its use in non-production atmospheres, such as testing and advancement. fft perimeter intrusion solutions.
Network Protection Approaches
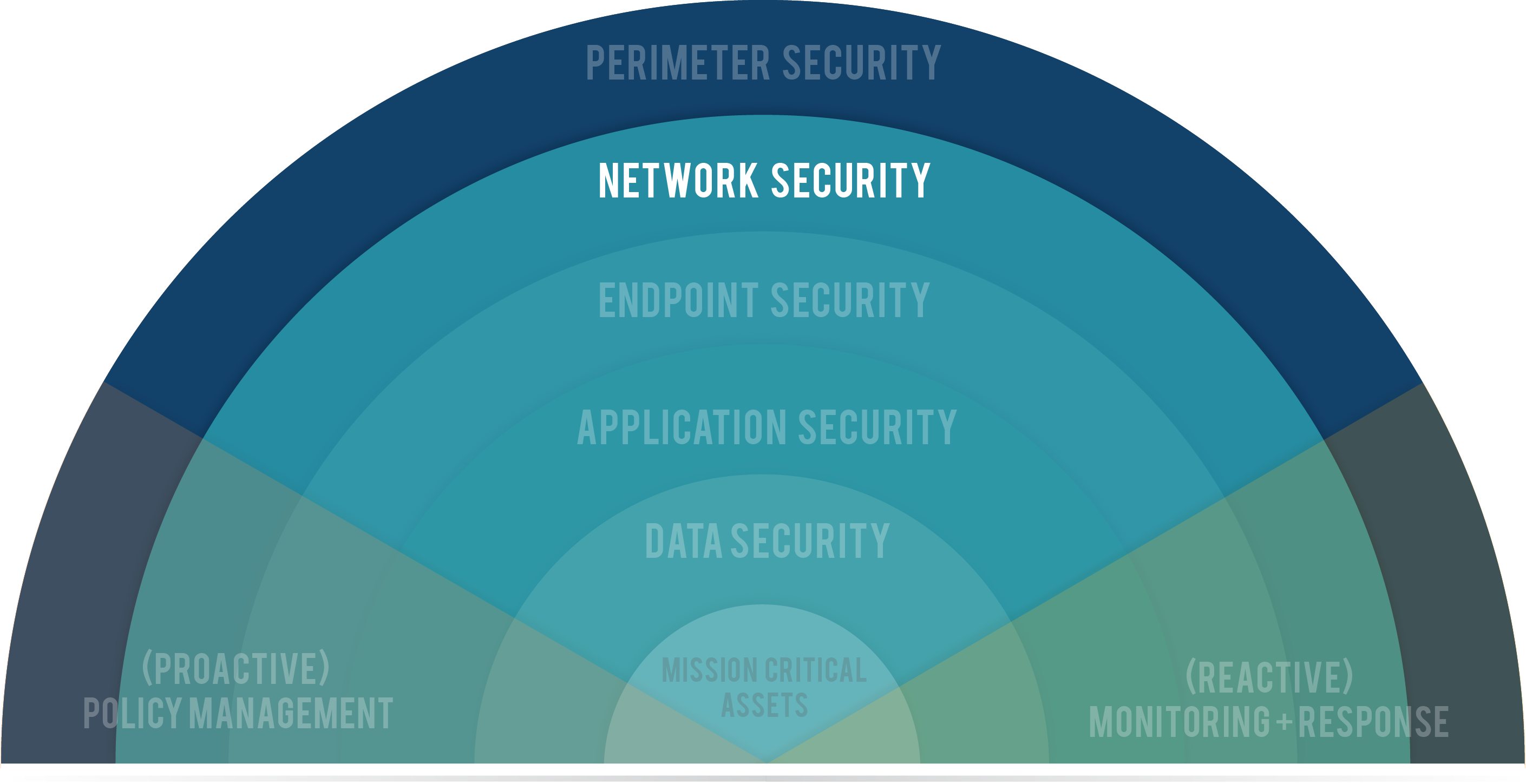
Applying durable network safety and security techniques is important for protecting a company's digital framework. These methods include a multi-layered approach that consists of both hardware and software program remedies created to safeguard the integrity, discretion, and accessibility of data.
One essential element of network safety and security is the deployment of firewall programs, which function as an obstacle in between trusted interior networks and untrusted external networks. Firewall programs can be hardware-based, software-based, or a mix of both, and they help filter outward bound and incoming website traffic based on predefined protection policies.
In addition, breach discovery and prevention systems (IDPS) play a crucial role in monitoring network web traffic for questionable tasks. These systems can notify managers to prospective violations and act to mitigate threats in real-time. On a regular basis updating and patching software application is additionally essential, as susceptabilities can be exploited by cybercriminals.
Moreover, implementing Virtual Private Networks (VPNs) guarantees safe and secure remote access, encrypting information sent over public networks. Lastly, segmenting networks can decrease the strike surface area and contain prospective violations, limiting their influence on the general facilities. By taking on these techniques, organizations can successfully strengthen their networks versus arising cyber dangers.
Ideal Practices for Organizations
Establishing ideal techniques for organizations is critical in preserving a strong protection stance. A detailed method to data and network protection begins with normal threat evaluations to identify susceptabilities and prospective threats.
In addition, constant employee training and recognition programs are necessary. Workers should be informed on recognizing phishing efforts, social engineering methods, and the value of adhering to protection protocols. Normal updates and patch news monitoring for software application and systems are additionally important to shield against recognized vulnerabilities.
Organizations have to test and establish incident action intends to make sure readiness for prospective violations. This includes establishing clear interaction channels and functions during a safety incident. In addition, information security must be utilized both at remainder and en route to protect delicate details.
Finally, carrying out routine audits and compliance checks will assist make sure adherence to well-known policies and relevant regulations - fft perimeter intrusion solutions. By adhering to these best practices, organizations can substantially boost their strength versus arising cyber threats and safeguard their important properties
Future Trends in Cybersecurity
As organizations navigate an increasingly complex digital landscape, the future of cybersecurity is poised to evolve considerably, driven by shifting and emerging innovations threat paradigms. One prominent trend is the integration of expert system (AI) and artificial intelligence (ML) right into protection structures, permitting real-time risk detection and feedback automation. These modern technologies can assess huge amounts of information to recognize abnormalities and prospective breaches more efficiently than typical techniques.
One more vital trend is the surge of zero-trust design, which requires continual verification of user identities and tool safety, regardless of their area. This technique reduces the risk of expert dangers and enhances defense against external strikes.
Moreover, the increasing fostering of cloud services necessitates durable cloud safety and security approaches that attend to unique susceptabilities connected with cloud settings. As remote work becomes a long-term fixture, securing endpoints will certainly likewise end up being paramount, bring about an elevated concentrate on endpoint discovery and reaction (EDR) remedies.
Finally, governing compliance will certainly proceed to shape cybersecurity methods, pressing organizations to embrace extra strict information protection procedures. Welcoming these trends will certainly be important for companies to strengthen their defenses and navigate the progressing landscape of cyber hazards efficiently.
Conclusion
To conclude, the application of robust information and network protection measures is important for companies to guard versus arising cyber hazards. By making use of security, accessibility control, and reliable network safety techniques, organizations can considerably decrease vulnerabilities and safeguard sensitive information. Adopting ideal techniques better enhances resilience, preparing organizations to encounter advancing cyber obstacles. As cybersecurity remains to progress, staying informed about future fads will certainly be essential in keeping a strong defense versus prospective risks.
In an era noted by the best site fast evolution of cyber hazards, the value of data and network security has never been extra noticable. As these risks end up being extra complex, comprehending the interaction in between information safety and security and network defenses click here for more info is crucial for mitigating risks. Cyber threats include a broad variety of destructive activities aimed at jeopardizing the discretion, integrity, and schedule of data and networks. An extensive technique to data and network safety and security starts with routine threat analyses to determine vulnerabilities and prospective hazards.In final thought, the application of robust data and network security measures is necessary for companies to protect against emerging cyber dangers.
Comments on “How Fiber Network Security Solutions Ensure Maximum Protection for Your Communications”